Cybersecurity Engineering
Strengthen Cybersecurity
Reduce risk through practical security engineering, controlled validation, and managed protection strategies that improve visibility, harden systems, and support real-world resilience.
Managed IT And Managed Security Services
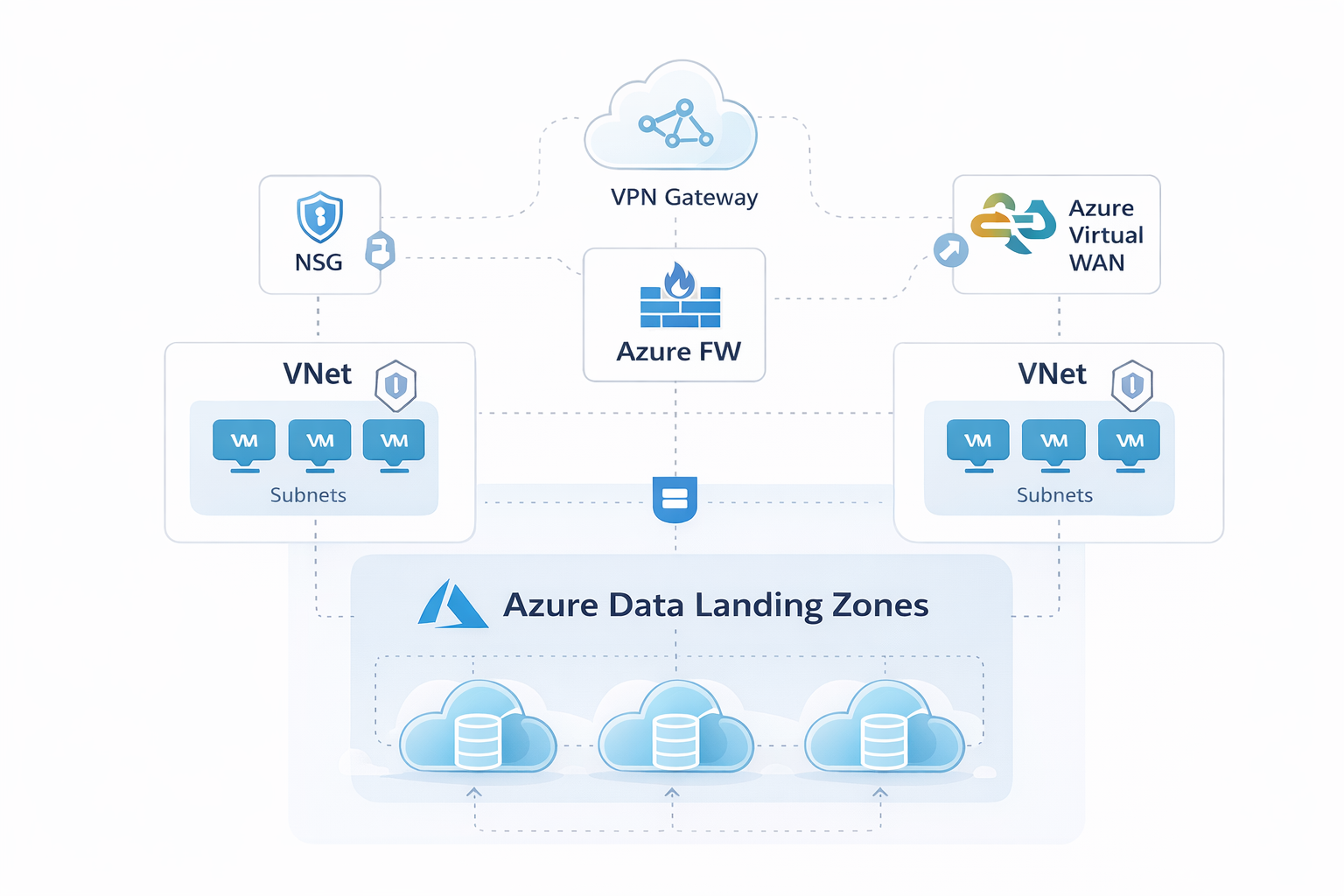
Azure Architecture, Migration, And Governance
Cybersecurity Engineering And Validation
CMMC Readiness And Compliance Support
Managed Security
MSSP + Engineering
Integrated security operations, hardening, and validation designed to improve defensive posture and reduce operational risk.
Security Validation
Controlled Testing
Authorized security testing used to confirm whether controls are working as intended and where remediation should be prioritized.